CAPTCHA is a security measure used in HTML forms to prevent spam submissions by distinguishing between human users and bots. The CAPTCHA field is added in HTML, but the generation and validation of the CAPTCHA code are done server-side. JavaScript enhances the user experience by performing client-side validation before form submission, but the actual validation should always be done server-side to ensure security.
Learn how HeroTofu handles form spam with CAPTCHA.
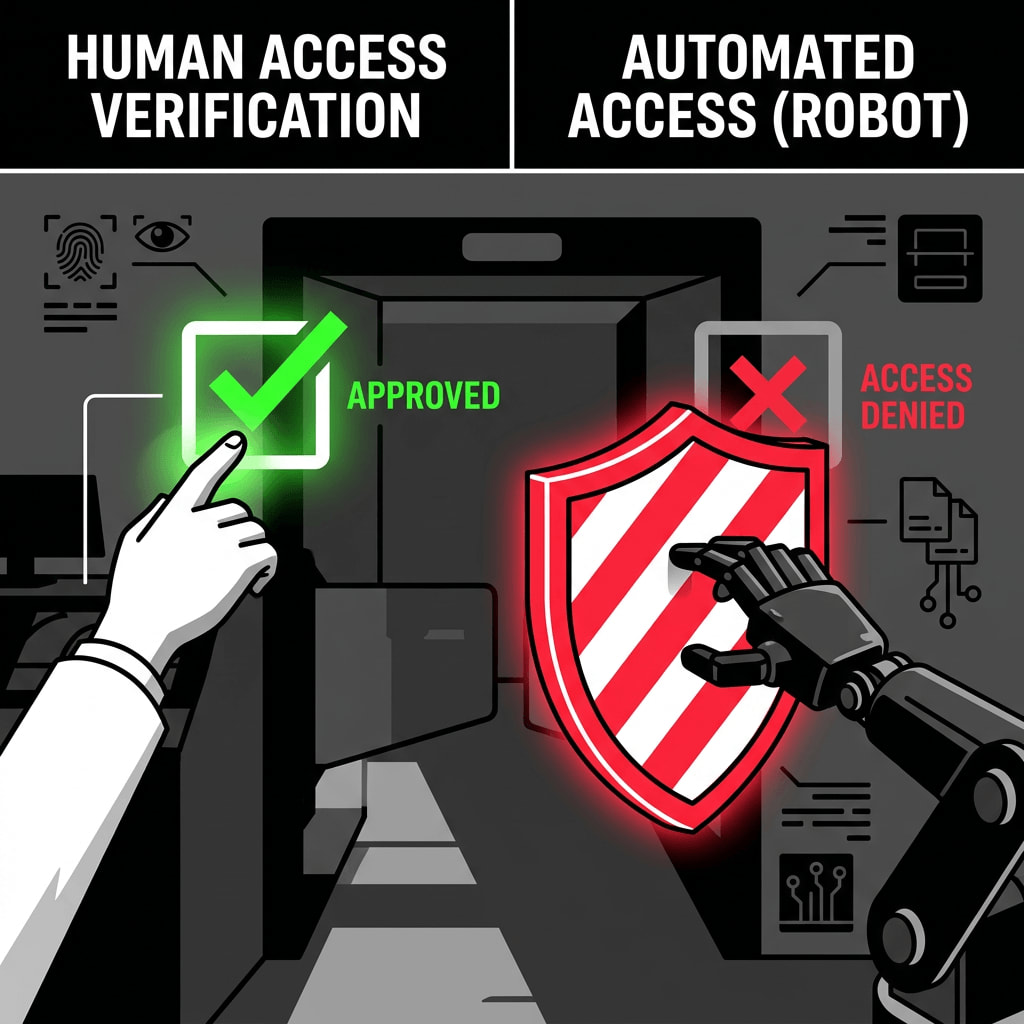
CAPTCHA, which stands for Completely Automated Public Turing test to tell Computers and Humans Apart, is a commonly used method to prevent spam submissions in HTML forms by distinguishing between genuine human users and automated bots. It's an essential security measure that can protect against potential threats such as spam or Distributed Denial of Service (DDoS) attacks.
In the context of HTML forms, a CAPTCHA field is usually added as an input element. However, the actual generation and validation of the CAPTCHA code are typically handled on the server-side. This is because client-side logic, including JavaScript, can be easily bypassed by a sophisticated bot.
When a form with a CAPTCHA is loaded, the server generates a unique CAPTCHA image and associates it with a session or unique token. This token is then embedded within the form as a hidden field or included in the CAPTCHA image URL. The server stores this token-value pair for later validation.
When the user submits the form, the server receives both the user's input and the associated token. The server then compares the user's input with the stored value for that token. If they match, the server accepts the form submission; otherwise, it rejects it.
JavaScript plays a significant role in the client-side validation of the form. It can prevent the form from being submitted if the CAPTCHA field is left empty, enhancing the user experience. However, it's important to remember that this is just a layer of convenience for the user, and the real validation should always be done server-side to ensure security.
Here is a more detailed example of how this process might work:
<form id="myForm" action="/submit" method="post">
<input type="text" name="username" required />
<input type="password" name="password" required />
<img id="captchaImage" src="/captcha?token=123456" alt="CAPTCHA Image" />
<input type="text" name="captcha" required />
<input type="hidden" name="token" value="123456" />
<button type="submit">Submit</button>
</form>
document.querySelector('#myForm').addEventListener('submit', function (event) {
var captchaField = document.querySelector('input[name="captcha"]');
if (captchaField.value === '') {
event.preventDefault();
alert('Please fill out the CAPTCHA!');
} else {
// Optionally, you could also refresh the CAPTCHA image here
document.querySelector('#captchaImage').src = '/captcha?token=' + new Date().getTime();
}
});
In this example, the CAPTCHA image URL includes a token, and the same token is embedded in the form as a hidden field. When the form is submitted, both the user's input and the token are sent to the server for validation.
Related terms:
HeroTofu is a set of tools and APIs designed to help Developers and Marketers.
© 2026 HeroTofu by Munero